Seeker
The industry's first interactive application security testing (IAST) software solution with active verification and sensitive-data tracking for web-based applications.
See how Seeker® IAST solutions help development, QA, DevOps, and security teams automate the security testing of modern web applications and services.
The recognized leader in web-based interactive application security testing
Gold for API Security
2023 Gartner® Magic Quadrant™ for Application Security Testing

Cybersec Asia 2020

Readers' Choice Awards 2021
Focus on real web-based application vulnerabilities
Our patented active verification technology
- Automatically retests identified application vulnerabilities and validates whether they are real and can be exploited
- Provides a real-time view of the top security vulnerabilities
- Delivers insights into the sensitive data flow and API calls for immediate remediation
Protect sensitive data
Sensitive-data tracking shows you where your most critical information and secrets are stored without sufficient encryption, helping ensure compliance with key industry standards and regulations, including PCI DSS and GDPR.

Integrate with CI/CD and DevOps workflows
Seeker is easy to deploy and scale in your CI/CD development workflows. Native integrations, web APIs, and plugins provide seamless integration with the tools you use for on-premises and cloud-, microservices-, and container-based development. You’ll get accurate results out of the box, without extensive configuration, custom services, or tuning.
Seeker monitors web app interactions in the background during normal testing and can quickly process hundreds of thousands of HTTP(S) requests, giving you results in seconds with near-zero false positives—no need to run manual security scans.

Secure APIs, microservices, and web services
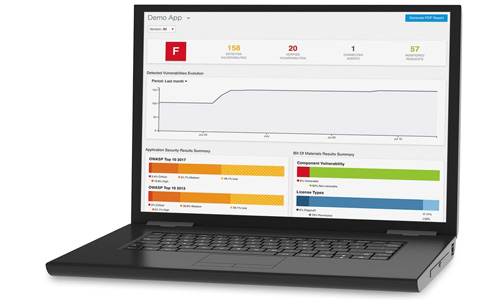
Seeker discovers all known and unknown APIs in your application portfolio, dynamically scans them for vulnerabilities, and reports on findings in visual dashboards. Seeker detects API and web interfaces, including microservices like gRPC, by finding specifications for REST, SOAP, and GraphQL APIs and verifying their security posture.

Streamline security compliance and remediation
Seeker makes security compliance reporting easy. Detailed dashboards show compliance with OWASP Top 10, PCI DSS, GDPR, and CWE/SANS Top 25, as well as alerts when applications expose sensitive information. Seeker also pinpoints vulnerable lines of code and provides detailed contextual remediation advice via e-learning, which helps your development teams learn and fix vulnerabilities quickly.
Identify risk in open source and third-party libraries
Seeker integrates Black Duck® Binary Analysis, which analyzes target binaries for open source security vulnerabilities, versioning, and license information and matches them against the knowledgebase in Black Duck Hub. You get a unified view of all identified vulnerabilities found in custom code and component libraries.
Seeker monitors web app interactions in the background during normal testing and can quickly process hundreds of thousands of HTTP(S) requests, giving you results in seconds with near-zero false positives—no need to run manual security scans.

We chose Seeker because testers and developers don’t need to invest time or have expertise in order to execute security tasks on a regular basis. Seeker provides correlation between vulnerabilities and impacted source code, saving developer effort.”
Secure your web apps with IAST
Seeker IAST
The State of API Security
Automating web security testing
Société Française du Radiotelephone